Anonymous employee survey controls guide (2026)
Employee feedback programs increasingly rely on anonymous employee survey controls to protect identity while collecting honest workplace input. Organizations across countries such as the US, the UK, and India face stricter expectations around workforce data governance, privacy safeguards, and transparency in feedback systems.
This guide explains the governance mechanisms, privacy architecture, and operational controls behind anonymous employee survey controls. The practices discussed here are tested and reviewed across SME and enterprise environments, helping organizations assess whether employee feedback platforms genuinely preserve anonymity and meet regulatory and trust requirements.
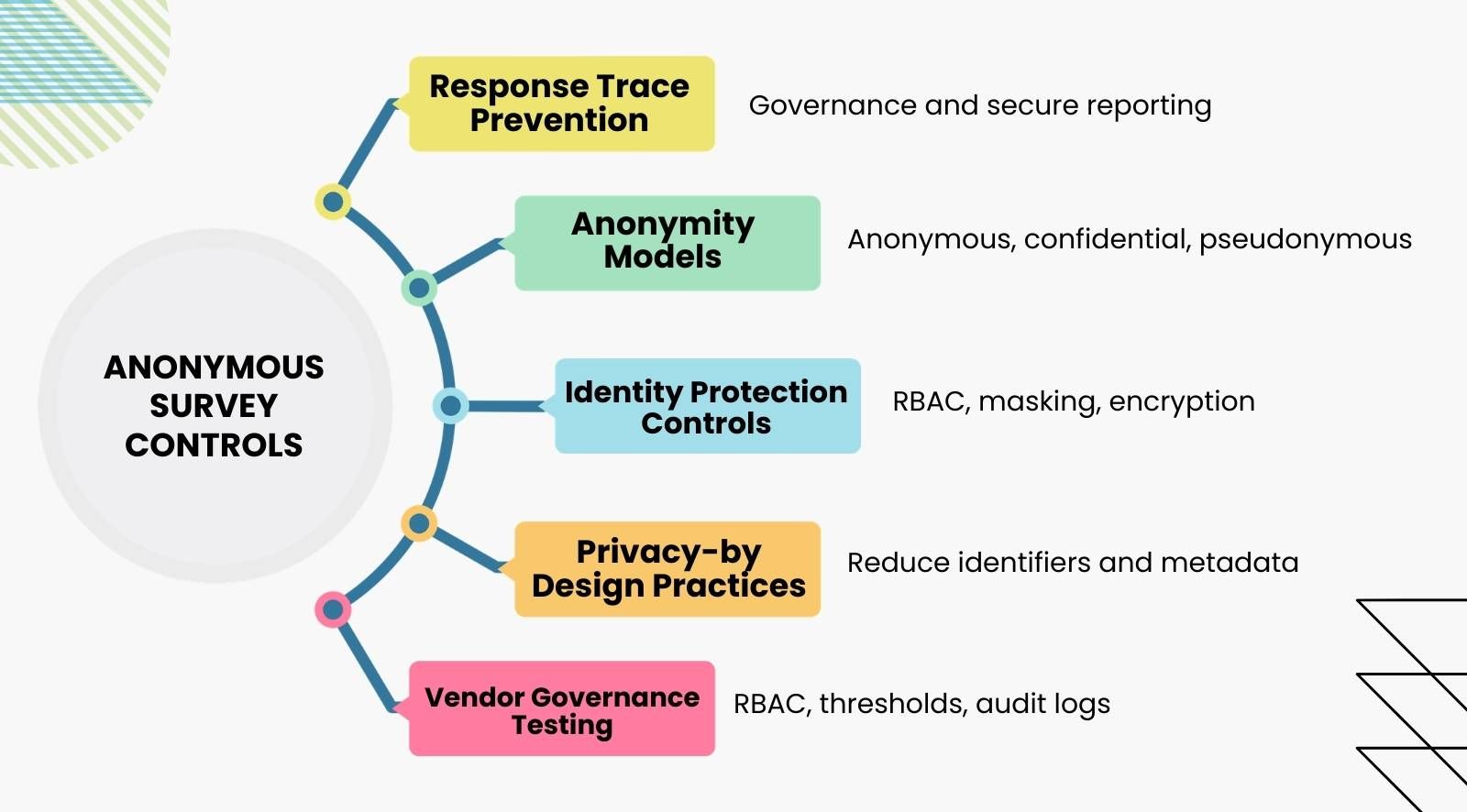
- Anonymous employee survey controls prevent responses from being traced to employees through governance, access controls, and secure reporting.
- Anonymous, confidential, and pseudonymous surveys differ in how identity data is stored and who can access it.
- RBAC, anonymity thresholds, encryption, masking, and audit logs protect employee identity.
- Privacy-by-design practices reduce metadata, limit identifiers, and secure survey submissions.
- Vendor demos should test RBAC, threshold enforcement, exports, comment masking, and audit logs.
What are anonymous controls in employee surveys?

Anonymous employee survey controls are governance and system mechanisms that protect respondent identity across the full survey lifecycle. These controls regulate how feedback is collected, processed, accessed, and reported so individual responses cannot be traced back to employees.
By reducing the risk of social desirability bias, anonymous employee survey controls allow employees to respond honestly without fear of judgment. They include access permissions, data protection layers, privacy-safe survey design, and secure reporting outputs.
Anonymity thresholds are only one element within anonymous employee survey controls. Thresholds block results when response counts are too small, while broader control systems govern identity protection across databases, analytics tools, and exports.
What is the difference between anonymous, confidential, and pseudonymous surveys?
Anonymous, confidential, and pseudonymous surveys represent three different identity protection models used in employee feedback systems.
How do role-based access controls (RBAC) protect anonymity in employee surveys?
Role-based access controls (RBAC) in anonymous surveys define how survey insights are accessed across different organizational roles. Whenever organizations survey employees, these controls ensure that survey responses remain confidential and that HR, managers, executives, and compliance teams see only the level of information required for their responsibilities.
To further protect respondent identity, anonymous employee survey controls enforce a minimum number of survey responses before results are shown, maintaining trust in the confidentiality of the feedback process through structured permissions.
1. Access by role
RBAC structures assign survey visibility according to job responsibility. HR teams typically administer surveys and monitor enterprise trends. Managers receive aggregated team insights, while executives view organization-level indicators. This structure allows leaders to act on feedback without exposing individual responses.
Typical RBAC access layers include:
- HR administrators managing survey configuration and enterprise analytics
- Line managers reviewing aggregated team engagement results from employee engagement surveys, including feedback on employee engagement and company initiatives
- Executives monitoring organization-wide engagement trends and insights from employee engagement surveys, with a focus on employee engagement and feedback on company initiatives
- Compliance teams verifying governance and privacy controls
Limiting access based on role prevents misuse of sensitive feedback data.
2. Identity protection
RBAC systems prevent identity exposure by separating survey data access across roles and data layers. By ensuring reports are completely anonymous, employees are more likely to share honest feedback. Managers view aggregated reports that meet anonymity thresholds, while individual response records remain inaccessible.
Advanced systems also restrict cross-filtering combinations that could reveal identity. For example, filtering results by small demographic groups or unique team attributes may automatically disable reporting if anonymity risks increase.
3. RBAC and thresholds
Anonymity thresholds and RBAC operate together to strengthen anonymous employee survey controls. Thresholds prevent reporting when response counts are too low, while RBAC ensures only authorized roles can view survey outputs that pass those thresholds.
For example, a manager may access results only if at least five team members respond. If participation drops below that level, the system withholds reporting until enough responses accumulate, protecting individual identities.
These anonymity thresholds are important for both one-off surveys, used for quick, informal, or standalone feedback, and regular surveys, such as scheduled quarterly or monthly check-ins, to maintain employee trust and encourage honest participation in anonymous feedback collection online.
4. Audit logging
Audit logging records all administrative and reporting activity within survey systems. Logs track events such as role changes, report downloads, and permission updates. These records provide traceability for how anonymous survey data is accessed. Audit logs can also track access to HR data derived from survey systems, ensuring all sensitive information is protected.
Strong anonymous employee survey controls maintain immutable audit trails that cannot be altered by administrators. Governance teams can review these logs during compliance checks to confirm that access rules and privacy protections were consistently enforced.
5. Governance value
RBAC is essential for maintaining governance in large organizations where multiple stakeholders analyze survey results. Without strict access controls, survey data could be exposed through unrestricted reporting or accidental downloads.
Enterprise survey systems, therefore, combine RBAC, anonymity thresholds, and audit monitoring to create layered identity protection. This architecture helps organizations collect honest employee feedback while maintaining trust, privacy, and compliance with internal data governance policies.
What data masking and output protection techniques protect survey anonymity?

Data masking and output protection techniques prevent employee identities from being exposed when survey data is analyzed, exported, or viewed in dashboards. These protections enable deeper analysis and more accurate insights from survey feedback without compromising anonymity.
These safeguards ensure individual responses remain protected while organizations access aggregated insights through structured anonymous employee survey controls, which is especially critical for manager feedback survey questions that evaluate leadership.
- Encryption of individual responses and aggregated outputs: Encryption protects survey inputs from unauthorized access during submission, storage, and processing. Modern survey systems encrypt individual responses while generating aggregated outputs through secure processing layers so analysts cannot access identity-linked raw data.
- Masking comment metadata to prevent indirect identification: Comment masking removes metadata such as timestamps, device data, or department markers that could reveal a respondent. Systems may also scan comments for names or identifiable references before displaying them in reports.
- Separation of raw data storage from reporting layers: Secure survey architectures store raw response data in protected databases while dashboards operate on processed datasets. This separation ensures reporting tools cannot access identity-linked records directly.
- Controlled exports and download safeguards: Export protection prevents survey data from exposing identities once downloaded. Systems enforce aggregated exports, remove metadata, and apply response thresholds to prevent reconstruction of individual responses in spreadsheets.
- Identity-safe dashboards and reporting filters: Dashboards include safeguards that block views likely to reveal individuals. If filters narrow data to very small groups, reporting is automatically disabled, or categories are merged to maintain anonymity.
What privacy by design principles protect anonymity in employee surveys?
Privacy by design principles in anonymous surveys ensure identity protection is built into the survey system architecture from the start. These principles are especially important for modern feedback tools such as pulse surveys, continuous listening platforms, and digital suggestion boxes, which rely on frequent, real-time, and anonymous input from employees, often using fun employee engagement questions to boost workplace morale.
It reduces the collection of identifiable data, restricts exposure during analysis, and supports anonymous employee survey controls that align with privacy regulations and employee trust expectations.
1. Minimizing identifiable metadata
Minimizing metadata reduces the risk of indirect identification in survey systems. Platforms should avoid storing information such as device identifiers, exact timestamps, IP addresses, or location data unless operationally necessary. Removing these attributes prevents identity reconstruction through technical metadata.
Tools like CultureMonkey can be configured to minimize metadata collection, supporting anonymity and offering more advanced safeguards than basic options like collecting anonymous employee feedback with Google Forms.
2. Safe field design without unique identifiers
Safe field design avoids survey questions that can uniquely identify respondents. Questions should not request employee IDs, specific job titles, or highly granular demographic information.
When including questions about work-life balance, a common topic in employee satisfaction surveys, ensure they are phrased to avoid collecting unique or identifying information, drawing from employee survey sample questions to consider in 2025 that prioritize privacy-safe wording.
3. Data minimization and responsible retention policies
Data minimization limits the amount of personal data collected and stored in survey systems. Organizations should retain only aggregated insights required for analysis and remove raw datasets after reporting cycles.
By retaining only aggregated data, organizations can focus on improving employee experience and making meaningful improvements based on survey results as part of broader workplace feedback mechanisms and processes. Clear retention policies reduce long-term privacy exposure and support regulatory compliance.
4. Secure survey submission architecture
Survey systems should use secure submission channels that prevent response interception or tracking. Secure internal communication channels, such as Slack or Microsoft Teams, should be used to distribute survey links and instructions to employees. Encryption protocols and secure authentication layers ensure employee responses cannot be traced through technical monitoring during the survey process.
What compliance frameworks and legal guardrails apply to anonymous employee survey controls?

Compliance frameworks and legal guardrails define how anonymous employee survey controls must protect workforce data under privacy regulations. Human resources teams play a key role in ensuring compliance and promoting employee satisfaction through anonymous survey practices that also inform a structured employee engagement calendar for 2025 and beyond.
These rules govern data collection, processing, storage, and vendor responsibilities to ensure employee feedback systems comply with legal standards across jurisdictions.
- GDPR requirements for anonymous feedback systems: The General Data Protection Regulation requires organizations to minimize personal data collection and ensure strong safeguards when employee feedback tools process identifiable information. True anonymity reduces regulatory exposure because anonymous data falls outside many GDPR personal data obligations.
- CCPA and regional privacy law considerations: Laws such as the California Consumer Privacy Act regulate how employee information is collected and disclosed. Anonymous survey systems help organizations avoid storing identifiable employee data, reducing risks linked to access requests, data disclosure obligations, and privacy complaints.
- Contractual safeguards with survey technology vendors: Organizations must ensure survey vendors follow strict data protection obligations through contractual agreements. These contracts should define data ownership, security responsibilities, and processing limits to maintain anonymous employee survey controls across third-party platforms.
- Data processing and controller responsibilities: Under many privacy frameworks, employers act as data controllers responsible for how survey information is collected and used. Survey vendors operate as processors and must handle data only under documented instructions defined in processing agreements.
- Cross-border data transfer protections: Employee feedback systems operating across multiple countries must ensure survey data transfers comply with international privacy regulations. Mechanisms such as standard contractual clauses or approved data transfer frameworks are often required for lawful cross-border processing.
- Legal defensibility through true anonymity design: Strong anonymous employee survey controls help organizations demonstrate that employee responses cannot be traced to individuals. This design reduces legal risk during investigations, employee disputes, or regulatory reviews by proving that identity-linked monitoring did not occur.
How do anonymous employee survey controls strengthen psychological safety and trust?

Anonymous employee survey controls strengthen psychological safety by ensuring employee feedback cannot be traced back to individuals. When employees feel their feedback is truly anonymous, it positively impacts company culture and trust, encouraging greater openness and engagement and amplifying the impact of broader employee engagement initiatives to maximize workplace engagement.
Clear privacy safeguards, governance rules, and transparent communication increase trust in survey systems and encourage employees to provide honest feedback without fear of identification or retaliation, which also improves the quality of employee engagement workshops that elevate workplace culture.
1. Trust through system design
Privacy-focused system architecture signals that employee feedback is protected through technical safeguards built into the survey platform. Organizations should proactively reassure employees about these technical safeguards to promote open communication and encourage honest feedback.
Encryption, strict access controls, and identity-safe reporting prevent responses from being traced to individuals. These protections strengthen anonymous employee survey controls and increase employee confidence in the feedback process.
2. Communicating anonymity clearly
Organizations should explain how anonymous employee survey controls protect identity before surveys begin. Communication should cover response thresholds, restricted access levels, and comment protections so employees understand how their responses remain anonymous.
3. Impact on participation
Survey participation increases when anonymity protections are visible and credible. Gallup survey emphasizes that reporting only aggregated results with minimum response thresholds is critical to building the trust needed for employees to respond honestly.
Maintaining strong anonymity protections not only builds trust but also encourages higher participation in future surveys.
4. Encouraging candid feedback
Clear anonymity safeguards encourage employees to provide honest feedback on leadership, workload, and workplace conditions. When employees know their identities are protected, they are more likely to provide negative feedback and honest answers without fear of retaliation.
Strong anonymous employee survey controls reduce fear of retaliation and help employees raise concerns that may otherwise remain unreported.
What are red flags in an anonymous survey control design?
Red flags in anonymous survey control design indicate weaknesses that may expose respondent identities or undermine trust in feedback systems. Organizations evaluating anonymous employee survey controls should review governance, access rules, and reporting safeguards to ensure anonymity protections cannot be bypassed.
Additionally, linking survey data to performance reviews can undermine anonymity protections and erode employee trust in the feedback process.
1. Lack of clear access rules
- Multiple roles can view detailed survey data without defined permission levels
- Managers or administrators can access raw responses instead of aggregated results
- Survey reporting access changes without formal governance approval
2. Manual overrides without governance
- Administrators can bypass anonymity thresholds manually
- Reporting restrictions can be disabled during analysis or exports
- No documented process exists for approving override actions
3. Export pathways that bypass privacy safeguards
- Survey data can be exported with individual responses or metadata
- Export files include timestamps, department identifiers, or small group data
- Spreadsheet exports allow reconstruction of individual responses through filtering
4. Weak audit logging and monitoring
- Survey systems do not track report downloads or data exports
- Permission changes are not recorded or monitored by governance teams
- Audit logs can be modified or deleted by system administrators
5. Overly granular filtering and segmentation
- Dashboards allow filtering results for very small teams or demographic groups
- Managers can combine filters that reveal identities indirectly
- Reporting tools do not automatically disable views that violate anonymity thresholds
How should organizations evaluate anonymous employee survey controls in vendor demos?
Organizations should evaluate anonymous employee survey controls in vendor demos by testing how identity protection works in real scenarios. Additionally, organizations should assess how the system manages constructive feedback in anonymous surveys, ensuring it supports open and actionable communication.
Vendors should demonstrate how access, exports, and reporting safeguards prevent identification. Strong systems show enforceable controls, while weak platforms rely on claims without technical verification.
1. Role-based access control verification
- Ask the vendor: “Can a manager view individual responses or only aggregated results?”
- Request a live demonstration showing manager-level dashboards.
- Test whether different roles see different reporting views.
Strong governance response: The system restricts individual data and shows only aggregated insights by role.
Weak response: Vendor explains restrictions verbally without demonstrating enforced access controls.
2. Anonymity threshold enforcement test
- Ask: “What happens when a team has fewer responses than the anonymity threshold?”
- Request a demo where reporting is attempted below the threshold.
- Test whether administrators can bypass the threshold manually.
Strong governance response: System blocks reporting automatically and prevents overrides.
Weak response: Administrators can disable thresholds or generate reports manually.
3. Export and reporting safeguard checks
- Ask: “What information appears in exported survey reports?”
- Request an export sample including comments and aggregated scores.
- Check if exports include timestamps, demographic identifiers, or small group data.
Strong governance response: Exports contain only aggregated insights with masked identifiers.
Weak response: Exports include detailed metadata that can reveal respondent identity.
4. Metadata and comment privacy evaluation
- Ask: “How does the system prevent identification through comments?”
- Test whether comment metadata, such as timestamps or department labels, appear in reports.
- Check if comment filtering or masking features exist.
Strong governance response: System removes or masks identifiable comment metadata automatically.
Weak response: Comments appear exactly as submitted with traceable contextual information.
5. Audit logging and governance transparency
- Ask: “Can administrators see a log of who accessed survey reports or exported data?”
- Request a demonstration of audit logs showing report access events.
- Verify whether audit records can be modified or deleted.
Strong governance response: Immutable audit logs record all access and export actions.
Weak response: No audit tracking or logs can be edited by administrators.
Conclusion
Trustworthy anonymous employee survey systems depend on both design intent and consistent execution. Many platforms claim anonymity, but real protection relies on enforceable controls for anonymous employee surveys, such as role-based access restrictions, audit logging, data masking, and export safeguards.
Effective anonymity architecture requires layered protections across survey design, governance policies, and reporting systems. CultureMonkey helps organizations implement these safeguards by applying structured, anonymous employee-survey controls across data collection, analytics, and reporting workflows, ensuring employee responses remain protected while leaders still gain reliable engagement insights.
FAQS
1. What is the difference between anonymous and confidential employee surveys?
Anonymous surveys collect responses without linking them to respondents, preventing follow-up on individuals. Confidential surveys store identities but restrict access to HR or investigators for case handling. The choice affects legal obligations and follow-up capability. Anonymity increases candor, while confidentiality supports remediation.
2. How do role-based access controls protect survey anonymity?
Role-based access controls limit who can view which views and at what granularity. By enforcing aggregated dashboards, disabling raw response access, and restricting drill-downs, RBAC prevents managers from tracing answers to individuals. Configurable roles, enforced thresholds, and permission audits ensure access rules are technically applied, not just promised.
3. What privacy controls should anonymous employee feedback tools have?
Tools should provide strong encryption in transit and at rest, enforce anonymity thresholds, mask comment metadata, implement RBAC, maintain immutable audit logs, apply data minimization and retention rules, and support contractual vendor safeguards. These controls together form enforceable anonymous employee survey controls for enterprise use.
4. Are anonymous employee surveys compliant with GDPR?
Truly anonymous surveys that irreversibly remove identifiers generally fall outside the GDPR's personal data obligations. If responses are pseudonymous or identifiable, GDPR applies and requires a lawful basis, DPIA, and controller/processor safeguards. Verify anonymization methods and seek local legal review when in doubt.
5. How does data masking protect anonymity in feedback tools?
Data masking removes or generalizes identifiers and sensitive metadata before analysis. Techniques include redacting names, truncating timestamps, tokenizing unique strings, and aggregating small groups. Masking prevents indirect identification through contextual clues and stops reconstruction of identities from exported datasets or dashboard filters.
6. Can audit logs help maintain anonymous survey governance?
Yes. Immutable audit logs record who accessed reports, exported data, or changed permissions. Routine log reviews and alerting detect misuse, manual overrides, or policy violations. Audit trails provide forensic evidence during disputes, support compliance reporting, and demonstrate that anonymous employee survey controls were enforced.
7. What are common red flags in alleged “anonymous” survey systems?
Look for these red flags: missing or bypassable anonymity thresholds, manual overrides without governance, exports containing timestamps or identifiers, editable or absent audit logs, overly granular filters that reveal individuals, and vague vendor responses about data handling or protections.
8. How should employers communicate anonymity safeguards to employees?
Communicate anonymity safeguards clearly before and after surveys: explain thresholds, who sees which reports, what metadata is removed, retention periods, and vendor safeguards. Use short FAQs, sample reports, and leadership statements. Transparency about controls and follow-up actions builds credibility and raises participation.
9. How do anonymous controls impact survey participation rates?
Credible anonymous controls raise participation and candor; weak or unclear protections suppress honest responses. Visible safeguards and transparent follow-up typically increase response rates and richer qualitative feedback, while perceived risk of identification reduces participation and encourages guarded answers.
10. What should I test in a vendor demo to verify anonymity governance?
In a demo, test RBAC by logging in as different roles; attempt reporting below thresholds; request export samples; inspect comment metadata handling; view audit logs for access and exports; ask about override governance and retention policies. Strong vendors demonstrate enforced controls, test data, and immutable logs; weak vendors cannot.









