Secure text messaging systems for anonymous employee feedback (2026)
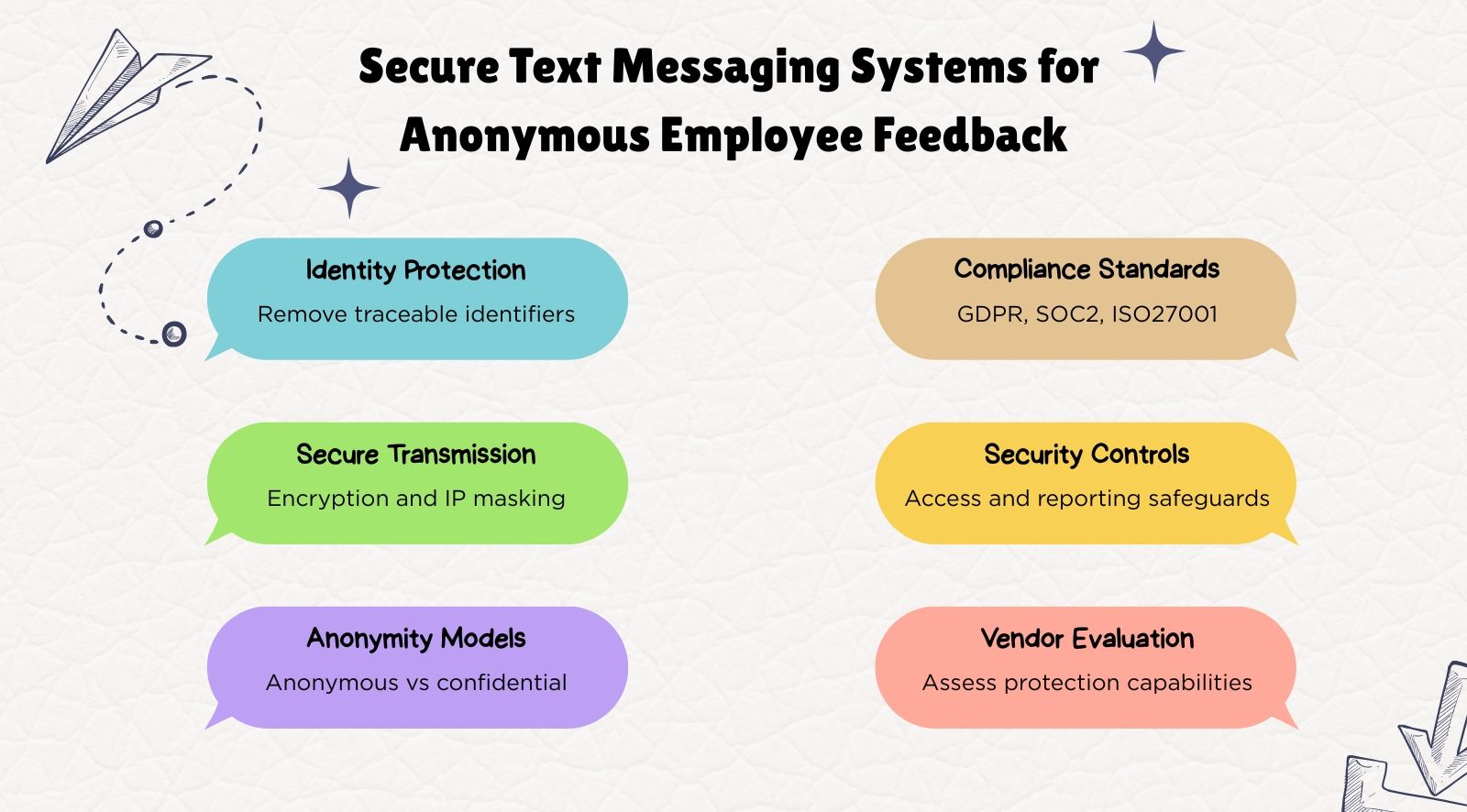
Secure text messaging systems for anonymous employee feedback help organizations collect employee input while protecting identity through encrypted and trace-free communication channels. As privacy regulations tighten across the United States, the United Kingdom, and India, organizations must ensure employee feedback data is handled securely and responsibly.
These systems enable employees to share honest workplace feedback without exposing personal identifiers such as IP addresses, device metadata, or login information. By combining encryption, identity protection, and restricted data access, they maintain true anonymity across feedback channels.
Secure text messaging systems are especially valuable for organizations with distributed workforces, helping them gather reliable employee insights while maintaining compliance with global privacy standards.
- Secure anonymous feedback systems protect employee identity by removing IP addresses, device metadata, and other traceable identifiers.
- End-to-end encryption, IP masking, and metadata stripping ensure responses remain untraceable during transmission and storage.
- Anonymous feedback differs from confidential feedback because anonymous systems store no identity data at all.
- Compliance standards like GDPR, SOC 2, and ISO 27001 ensure feedback systems follow strict data protection and security controls.
- Organizations should evaluate tools for encryption, identity protection, access controls, and reporting thresholds before deployment.
What makes anonymous feedback truly secure?
Anonymous feedback is secure when employee responses cannot be traced back to individuals through technical identifiers, system logs, or comprehensive reporting patterns. A secure, anonymous employee feedback tool removes identity signals and ensures responses cannot be linked to employees at any stage of the survey process.
Secure text messaging systems for anonymous employee feedback also reduce the administrative burden on HR teams by automating technical safeguards and compliance processes.
True anonymity depends on a system design that prevents identity reconstruction through data access, response patterns, or administrative controls. Employee text messaging systems for anonymous feedback must ensure that even administrators cannot connect responses to specific employees.
Organizations also rely on identity-safe reporting practices to maintain anonymity. Response thresholds, aggregated reporting, and controlled data access prevent identification in small teams. These safeguards allow organizations to collect honest feedback while project employee private conversations, making secure anonymous feedback systems an effective tool for promoting trust and openness in the workplace.
What technical safeguards protect anonymous employee feedback systems?
Secure anonymous feedback systems are protected through technical safeguards that prevent employee identities from being exposed through network logs, system data, or hidden identifiers. Encryption, IP masking, and metadata stripping remove traceable signals and protect survey responses during collection and storage across digital feedback systems.
Secure text messaging systems for anonymous employee feedback rely on layered security controls to maintain anonymity. Organizations using an anonymous employee feedback tool must combine encryption, IP masking, and metadata removal to ensure survey responses cannot be traced back to employees.
Additionally, it also supports essential features such as compliance, management tools, and integration with existing tech stack and existing HR systems. Reliable message delivery and seamless integration with communication tools are critical for an effective feedback collection process.
1. End-to-end encryption
End-to-end encryption protects survey responses while they travel between employee devices and survey servers. Encryption ensures that feedback data cannot be intercepted or read during transmission. Secure anonymous employee feedback tools also encrypt stored responses, preventing unauthorized access if the infrastructure is compromised.
2. IP masking and network anonymization
IP masking prevents survey platforms from storing the network address of respondents. Without this safeguard, responses could be traced to employee devices or office networks. Secure text messaging systems for anonymous employee feedback block or anonymous IP logging to prevent identity tracing.
3. Metadata stripping
Digital responses often contain hidden metadata such as browser fingerprints, timestamps, and device identifiers. Metadata stripping removes these technical markers before storing survey responses. This prevents indirect identification through device signatures or response patterns.
4. Role-based access controls
Role-based access controls restrict who can view survey data within the platform. Enterprise anonymous feedback tools limit access to aggregated insights while preventing administrators from viewing identifiable response records. Controlled access reduces internal exposure risks.
What is the difference between anonymity and confidentiality in employee feedback security?

Anonymity and confidentiality differ in how employee identity is handled in feedback systems. Anonymous feedback removes identifiers so responses cannot be linked to individuals, and these systems avoid collecting personal data to maintain true anonymity.
Confidential feedback stores identity information but restricts access to authorized investigators.
Organizations using an anonymous employee feedback tool must ensure identity signals such as IP addresses, device metadata, and login identifiers are removed. Secure text messaging systems for anonymous employee feedback rely on anonymity to keep responses untraceable.
HR teams are responsible for ensuring that feedback systems do not store unnecessary identifiers and maintain strict privacy standards.
What compliance requirements must anonymous feedback systems meet?
Anonymous feedback systems must comply with data protection standards that secure employee survey data and prevent identity tracing. Frameworks such as GDPR and SOC 2 require encryption, strict access controls, and documented data governance so organizations can deploy an anonymous employee feedback tool securely.
To fully meet regulatory standards, platforms should offer enterprise-grade security and essential features, including seamless integration with existing HR systems.
How can organizations evaluate the security of an anonymous feedback tool?

Organizations evaluate the security of an anonymous employee feedback tool by verifying whether the system prevents identity tracing through identifiers, system logs, or metadata. HR and IT teams must confirm that encryption, IP masking, metadata removal, and access controls protect feedback across the survey lifecycle.
HR and IT teams can use the following security evaluation framework when selecting secure text messaging systems for anonymous employee feedback.
- Verify encryption standards: Check whether survey responses are encrypted during transmission and storage. Secure anonymous feedback tools should use modern encryption protocols to prevent unauthorized access or interception.
- Check IP masking policies: Confirm that the platform does not store respondent IP addresses. An anonymous employee survey tool should prevent network tracing so employee responses cannot be linked to devices or office locations.
- Confirm metadata removal mechanisms: Ensure the platform removes browser fingerprints, device identifiers, and timestamps before storing responses. Secure employee feedback software should eliminate metadata that could reveal respondent identity.
- Assess anonymity thresholds in reporting: Survey dashboards should display results only after a minimum number of responses. This prevents managers from identifying employees in small teams or low-response groups.
- Review access control architecture: Verify that role-based permissions limit who can view survey data. Secure systems should present aggregated insights while preventing administrators from accessing identifiable response records.
In addition to these security measures, features like real-time analytics and recurring reminders are valuable for monitoring employee engagement and ensuring timely feedback. Real-time analytics allow organizations to track message delivery, engagement, and feedback trends instantly, supporting immediate decision-making.
Recurring reminders help automate notifications and encourage consistent participation. Integration with the existing tech stack further streamlines the feedback process by enabling seamless automation, data centralization, and ease of use.
What are the red flags that an anonymous feedback system isn’t secure?

An anonymous feedback system is not secure if responses can be traced through identifiers such as IP logs, device metadata, or identifiable reporting patterns. Collecting personal data is a major red flag for anonymous feedback systems, as it can compromise confidentiality and deter genuine responses. These weaknesses expose employee identity and reduce trust in feedback systems.
Organizations must detect these risks before deploying an anonymous employee feedback tool. The following indicators highlight common security gaps and underscore the need for enterprise-grade security to prevent data breaches and identity exposure.
IP addresses or device identifiers are stored
A major red flag is when the system records IP addresses or device fingerprints with survey responses. These identifiers can link feedback to employee devices or office networks. A secure anonymous employee feedback tool should automatically mask or discard network identifiers before storing responses.
If IP data is retained in system logs, administrators may still access network traces even when dashboards appear anonymous. Secure text messaging systems for anonymous employee feedback must block IP logging completely to prevent identity reconstruction through infrastructure data.
Metadata is retained with responses
Digital responses often include metadata such as browser signatures, timestamps, operating system details, and device characteristics. If this metadata is stored alongside feedback responses, analysts may identify respondents through device patterns or submission timing.
Secure anonymous feedback tools remove metadata before saving survey data. Metadata stripping prevents hidden identifiers from revealing employee identity through technical signals that remain invisible to standard reporting dashboards.
No anonymity threshold for reporting
Survey systems that show results with very few responses create a risk of employee identification. Managers may infer which employees submitted feedback when the team size is small or the response counts are low.
Secure anonymous employee feedback tools enforce reporting thresholds before displaying results. These safeguards ensure insights only appear after a minimum number of responses is reached, preventing identification through deduction.
Administrators can access raw response logs
If administrators can view raw survey logs or response-level data, anonymity may be compromised internally. Access to raw records can expose timestamps, submission patterns, or technical identifiers.
Secure employee feedback software restricts administrative visibility through role-based access controls. HR and leadership teams should only see aggregated insights instead of individual response records.
Survey links contain identifiable tracking parameters
Some feedback systems embed employee IDs or tracking tokens in survey links. These parameters allow platforms to associate responses with specific users even when surveys appear anonymous.
Secure text messaging systems for anonymous employee feedback avoid identity-linked URLs. Anonymous survey links should use non-identifiable tokens or randomized access methods that prevent user tracking.
Encryption practices are unclear or undocumented
If the platform does not clearly document encryption standards, survey responses may be vulnerable during transmission or storage. Weak encryption increases the risk of data interception or unauthorized access.
Secure anonymous employee feedback tools use modern encryption protocols for both data transmission and storage. Transparent documentation of encryption practices helps organizations verify the security of feedback infrastructure.
What should IT teams know about secure messaging and text-based feedback systems?

Secure messaging allows employees to submit feedback through SMS or anonymous reporting channels while maintaining anonymity. Secure text messaging systems for anonymous employee feedback must prevent identity tracing through phone numbers, device metadata, or routing logs. Strong architecture ensures responses remain anonymous during collection and analysis.
HR and IT teams must evaluate the infrastructure of any anonymous employee feedback tool before deployment. Messaging-based feedback introduces additional security risks if identity signals remain in system logs. The following framework helps organizations assess whether anonymous feedback software protects employee identity.
Encryption and message transmission security
- Transport layer encryption for all message traffic between employee devices and survey servers
- Encryption of survey responses during storage to prevent unauthorized system access
- Secure SMS gateway integration that prevents message interception or identity exposure
- End-to-end encryption across employee texting channels used for feedback collection
Identity protection and anonymity safeguards
- Phone numbers are anonymized or tokenized before feedback responses are stored
- Feedback databases do not store employee identifiers alongside responses
- Metadata, such as message headers or routing identifiers, is removed before storage
- Messaging systems prevent tracing responses through device identifiers or network logs
Access controls and system governance
- Role-based permissions restrict who can access survey dashboards or system data
- Raw response data is hidden from administrators, and only aggregated insights appear
- Audit logs track system activity without exposing employee identity
- Administrative permissions limit data exports and configuration changes
Compliance and infrastructure verification
- Platform demonstrates compliance with GDPR and SOC 2 data protection standards
- Regional data hosting options support regulatory requirements across countries
- Independent security audits validate the infrastructure used by the feedback system
- Documented security architecture explains encryption and identity protection methods
Anonymous reporting and response protection
- Survey dashboards enforce minimum response thresholds before results appear
- Analytics display aggregated insights instead of individual response records
- Data exports remove technical identifiers that could reveal respondent identity
- Reporting architecture prevents managers from identifying respondents in small teams
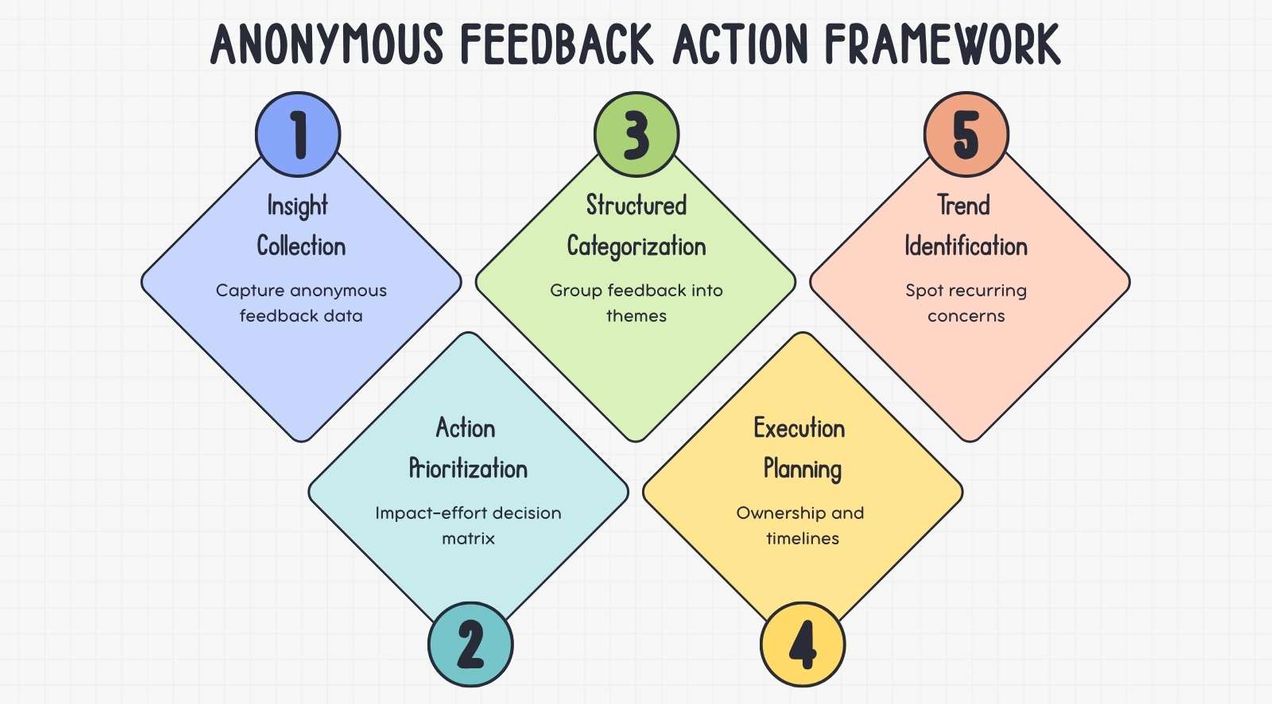
How can organizations build an anonymous trust architecture for employee feedback?

An anonymity trust architecture is a structured system of technical controls, governance policies, and effective employee communication practices that protect employee identity during feedback collection. Creating a workplace culture where employees feel safe to speak up is essential for improving engagement.
Organizations must combine secure infrastructure with clear privacy policies. This ensures employees trust secure text messaging systems for anonymous employee feedback.
Trust in anonymous feedback systems depends on visible privacy protections. SHRM research shows that over 70% of employees are more likely to share honest opinions when anonymity is assured. Gallup notes anonymous surveys boost participation by 20%.
Organizations can boost engagement by regularly conducting pulse surveys and using communication tools that make it easy to collect anonymous feedback. Collecting feedback regularly helps track trends over time and identify potential issues early. Organizations communicating these protections see higher engagement and actionable insights.
Establish strong technical identity protections
Organizations should deploy feedback platforms that remove identity signals before storing responses. Encryption, IP masking, and metadata stripping help prevent responses from being linked to employee devices or network logs.
Secure text messaging systems for anonymous employee feedback must also anonymize phone numbers and messaging identifiers. Identity-safe architecture ensures feedback remains anonymous across digital survey channels.
Implement governance and access controls
Privacy governance ensures anonymous feedback systems remain secure over time. Organizations should define who can access survey dashboards, configure reporting thresholds, and manage survey infrastructure.
Role-based access controls limit visibility to aggregated insights instead of raw response data. Strong governance policies prevent internal misuse and protect employee anonymity.
Communicate anonymity protections to employees
Employees must understand how their identity is protected before they trust feedback systems. Organizations should explain encryption practices, anonymity thresholds, and data protection policies when launching an anonymous feedback tool.
Transparent communication strengthens participation rates and reduces fear of retaliation. When employees understand that feedback cannot be traced, response rates and feedback quality typically improve.
Conclusion
Secure anonymous feedback systems like CultureMonkey help organizations collect employee input while protecting identity across digital survey channels. Encryption, IP masking, metadata stripping, and access controls prevent responses from being traced to individuals. Secure employee text messaging apps for anonymous feedback help collect reliable insights without exposing employee identity.
When supporting a global workforce, it is critical that these systems offer essential features and enterprise-grade security. These ensure regulatory compliance, protect sensitive information, and provide the robust management tools and integrations needed for an effective communication strategy across diverse teams and regions.
Organizations must evaluate security architecture, compliance standards, and governance before deploying an anonymous employee feedback tool. Strong encryption, identity protection, and transparent privacy practices build employee trust and improve participation in feedback programs.
Book a demo with CultureMonkey.
FAQS
1. How do anonymous feedback tools protect employee identity?
Anonymous employee feedback tools protect identity by removing identifiers such as IP addresses, device metadata, and login data from survey responses. Encryption protects data in transit and storage, while reporting thresholds and access controls protect anonymity and employee privacy, allowing employees to provide feedback and speak freely without negative consequences.
2. What compliance standards should an anonymous feedback tool meet?
A secure anonymous feedback texting platform should comply with GDPR, SOC 2 Type II, and ISO 27001. These compliance features require encryption, strict access controls, and documented data protection processes that safeguard employee privacy while enabling organizations to collect employee sentiment and generate meaningful insights.
3. Can anonymous survey responses be traced back to employees?
Properly designed anonymous feedback systems prevent responses from being traced back to employees. Secure platforms remove IP addresses, strip metadata, and avoid storing identifiers. This ensures feedback remains completely anonymous so employees can share honest responses that support improving workplace culture and employee experience.
4. What is metadata stripping in anonymous feedback systems?
Metadata stripping removes hidden technical information such as browser details, device identifiers, timestamps, and operating system data from survey responses. This protects anonymity by preventing administrators from identifying respondents through device fingerprints or technical patterns that could reveal employee identity.
5. How do you evaluate whether an anonymous feedback tool is truly secure?
Evaluate security by reviewing encryption, IP masking, metadata stripping, and access controls. A secure texting platform should also include compliance features such as GDPR or SOC 2 certification, real-time reporting, detailed reports, and AI-powered analytics that help leaders analyze employee sentiment without exposing individual responses.